Feds Disrupt Massive IoT Botnets Behind Record‑Breaking DDoS Attacks
Federal agencies dismantle four major IoT botnets behind massive DDoS attacks, disrupting millions of infected devices across the U.S., Canada, and Germany.

Authorities in the United States, Canada, and Germany have dismantled the online infrastructure powering four major Internet of Things (IoT) botnets responsible for millions of infections and some of the largest distributed denial‑of‑service (DDoS) attacks ever recorded. According to the U.S. Justice Department, the botnets — Aisuru, Kimwolf, JackSkid, and Mossad — collectively compromised more than three million IoT devices, including routers, security cameras, and other connected hardware.
These botnets were capable of launching overwhelming DDoS attacks that could knock virtually any online service offline, and investigators say the operators frequently used them to extort victims for money.
How the Botnets Operated
Federal Seizures and Infrastructure Takedown
The Justice Department revealed that the Department of Defense Office of Inspector General’s Defense Criminal Investigative Service (DCIS) executed seizure warrants targeting U.S.-based domains, virtual servers, and other infrastructure used to direct attacks — including those aimed at DoD‑owned IP addresses.
Investigators allege that the individuals behind the botnets launched hundreds of thousands of DDoS attacks, often demanding extortion payments. Some victims reported tens of thousands of dollars in losses and recovery costs.
Attack Volume by Botnet
| Botnet | Estimated Attack Commands |
|---|---|
| Aisuru | 200,000+ |
| JackSkid | 90,000+ |
| Kimwolf | 25,000+ |
| Mossad | ~1,000 |
A Coordinated International Operation
Global Law Enforcement Collaboration
The DOJ emphasized that the takedown was designed to halt further infections and cripple the botnets’ ability to launch future attacks. The operation involved:
- DCIS investigators
- The FBI’s Anchorage Field Office
- Nearly two dozen private‑sector technology partners
- Law enforcement agencies in Canada and Germany
“By working closely with DCIS and our international law enforcement partners, we collectively identified and disrupted criminal infrastructure used to carry out large-scale DDoS attacks,” said Rebecca Day, Special Agent in Charge of the FBI Anchorage Field Office.
Aisuru, Kimwolf, and the Evolution of IoT Malware
Rapid Growth and Advanced Infection Techniques
Aisuru, the oldest of the four botnets, emerged in late 2024 and quickly became notorious for launching massive DDoS attacks. By mid‑2025, it was infecting new IoT devices at an explosive rate.
In October 2025, Aisuru was used to seed Kimwolf, a more advanced variant that introduced a novel spreading mechanism capable
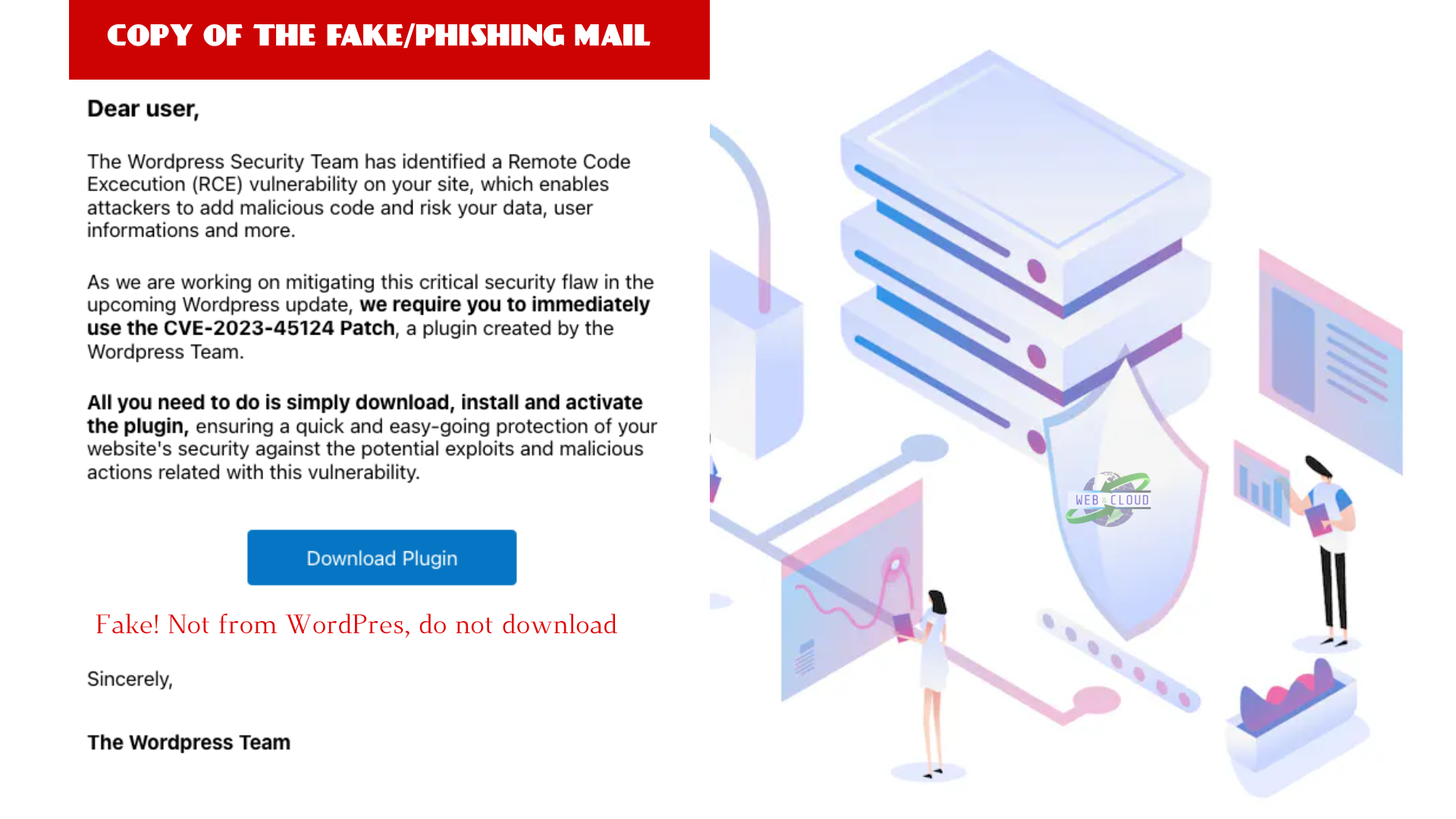
FAQ: IoT Botnets and the Recent Takedown
What is an IoT botnet?
An IoT botnet is a network of compromised Internet‑connected devices — such as routers, webcams, and smart appliances — controlled remotely by attackers to perform malicious activities like DDoS attacks.
What is a DDoS attack?
A Distributed Denial‑of‑Service (DDoS) attack floods a target server or network with overwhelming traffic, rendering it inaccessible to legitimate users.
How did these botnets infect devices?
Botnets like Aisuru and Kimwolf exploited vulnerabilities in IoT devices, often targeting weak passwords, outdated firmware, or unpatched security flaws. Kimwolf introduced a new method that allowed it to infect devices behind internal networks.
Why were these botnets so dangerous?
They were capable of launching record‑breaking DDoS attacks, extorting victims, and rapidly spreading across millions of devices worldwide.
Did the takedown stop the botnets completely?
The DOJ’s actions significantly disrupted their infrastructure and prevented further infections. However, IoT botnets are an ongoing global threat, and new variants often emerge.
How can users protect their IoT devices?
-
Change default passwords
-
Keep firmware updated
-
Disable unnecessary remote access features
-
Use strong network security settings
Reward this post with your reaction or TipDrop:
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 TipDrop
0
TipDrop
0