Iran‑Backed Hackers Claim Massive Wiper attack on Stryker: What We Know So Far
Iran‑backed hackers hit Stryker with a massive wiper cyberattack, disrupting global operations and raising concerns over healthcare supply chain impacts.
A hacktivist group aligned with Iranian intelligence has claimed responsibility for a large‑scale wiper cyberattack targeting Stryker, one of the world’s largest medical technology companies. The incident has disrupted operations across multiple countries, forced thousands of employees offline, and raised concerns about potential impacts on global healthcare supply chains.
Key Takeaways
- Handala, an Iran‑linked hacktivist group, claims to have wiped 200,000+ devices belonging to Stryker.
- Stryker reportedly shut down offices in 79 countries and sent home 5,000+ employees in Ireland alone.
- The attack appears to have leveraged Microsoft Intune to remotely wipe devices.
- Healthcare providers in the U.S. are already reporting supply chain delays for surgical equipment.
- The attack was allegedly retaliation for a February 28 missile strike in Iran.
Who Is Behind the Attack?
Handala (Handala Hack Team)
The group claiming responsibility, Handala, is a hacktivist organization linked to Iran’s Ministry of Intelligence and Security (MOIS). According to cybersecurity researchers, Handala is one of several personas associated with Void Manticore, a known MOIS‑affiliated threat actor.
Motivation
Handala states the attack was retaliation for a missile strike on an Iranian school on February 28 that killed at least 175 people. A U.S. military investigation cited by major news outlets reportedly attributes the strike to the United States.
What Happened to Stryker?
A Global Disruption
Stryker — a Michigan‑based medical technology giant with 56,000 employees in 61 countries — experienced a sudden and severe outage affecting its global network. Employees in Ireland, the company’s largest hub outside the U.S., were sent home after systems went down.
Wiper Attack Claim
Handala claims to have:
- Wiped 200,000+ systems, servers, and mobile devices
- Forced shutdowns in 79 countries
- Stolen data now “in the hands of the free people of the world”
Device Wipes via Microsoft Intune
Sources familiar with the incident say the attackers may have used Microsoft Intune, a legitimate enterprise device‑management tool, to issue remote wipe commands across Stryker’s fleet of devices. This is supported by employee reports on Reddit urging staff to uninstall Intune immediately.
Impact on Employees and Operations
Ireland: 5,000+ Workers Sent Home
Reports indicate:
- All network‑connected systems are down
- Employees’ personal phones with Microsoft Outlook installed were remotely wiped
- Device login screens were defaced with the Handala logo
U.S. Headquarters
A voicemail at Stryker’s Michigan headquarters states the company is experiencing a “building emergency,” suggesting significant operational disruption.
Potential Healthcare Supply Chain Fallout
Stryker’s Role in Healthcare
Stryker is a major supplier of:
- Surgical tools
- Implants
- Emergency medical equipment
- Hospital systems (including LifeNet for ECG transmission)
Early Signs of Disruption
A U.S. healthcare professional reported being unable to order surgical supplies normally sourced from Stryker — a serious concern given the company’s widespread presence in American hospitals.
American Hospital Association (AHA) Response
The AHA says it is monitoring the situation but has not yet confirmed widespread disruptions. However, it warns that this could change if the outage persists.
Hospitals Disconnecting from Stryker Systems
A memo from Maryland’s EMS agency states that hospitals are disconnecting from Stryker’s online services, including LifeNet, which paramedics rely on to transmit EKGs. Hospitals are being instructed to use radio consultation if ECG transmission is unavailable.
Why This Attack Matters
A Real‑World Supply Chain Attack
This incident highlights how cyberattacks on medical technology companies can have immediate, real‑world consequences:
- Delayed surgeries
- Slower emergency response
- Disrupted medical device logistics
- Potential patient safety risks
Geopolitical Cyber Warfare
The attack underscores the growing trend of state‑aligned hacktivism, where politically motivated groups target critical infrastructure to retaliate for military actions.
What Happens Next?
This is a developing story, and Stryker has not yet released a detailed public statement. Key questions remain:
- How much data was actually stolen or destroyed?
- How long will global operations be disrupted?
- Will hospitals face significant shortages?
- Will the attack trigger regulatory or governmental intervention?
Updates will likely emerge as Stryker restores systems and investigators assess the full scope of the breach.
Frequently Asked Questions on the Stryker's Cyberattack
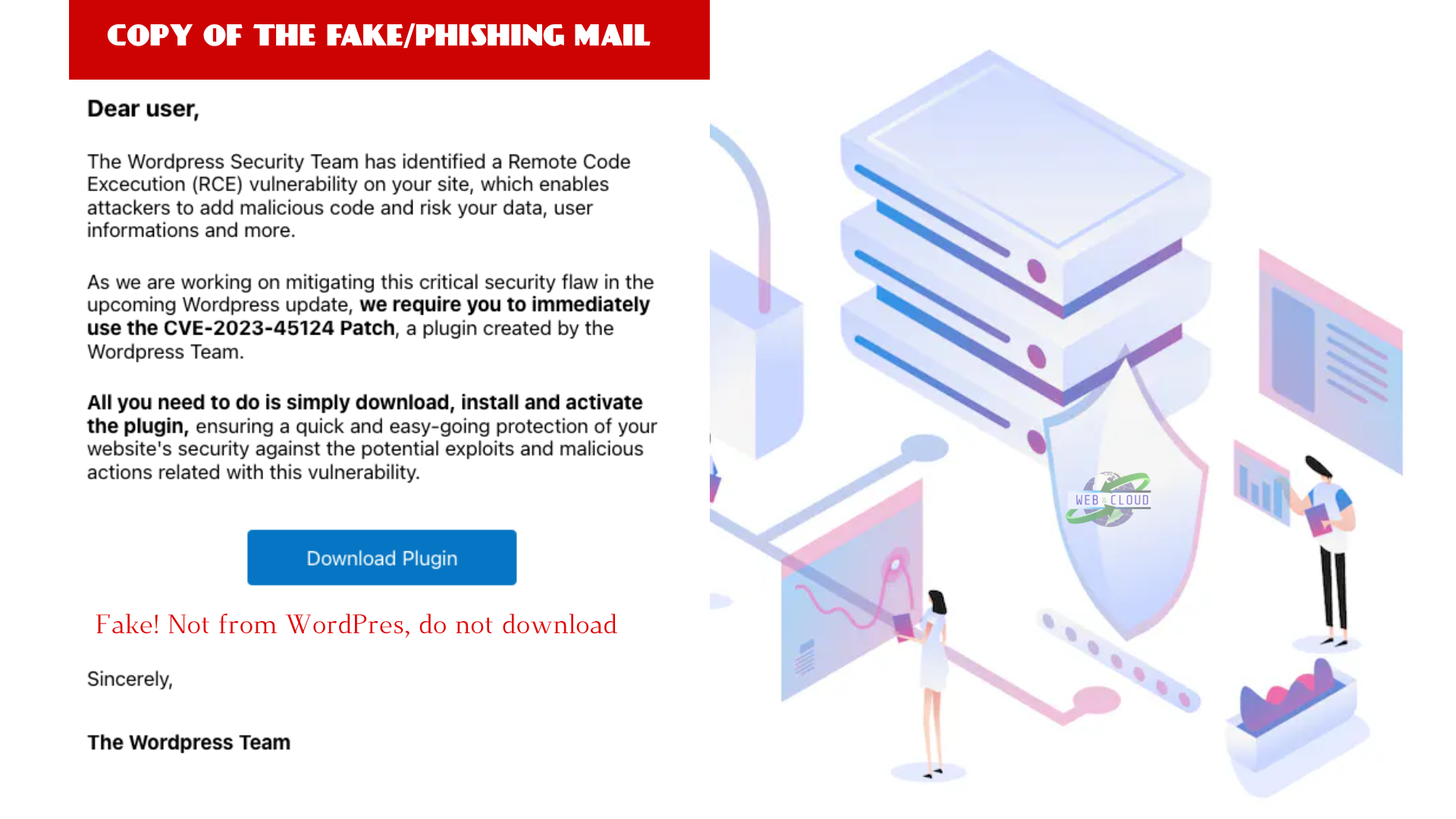
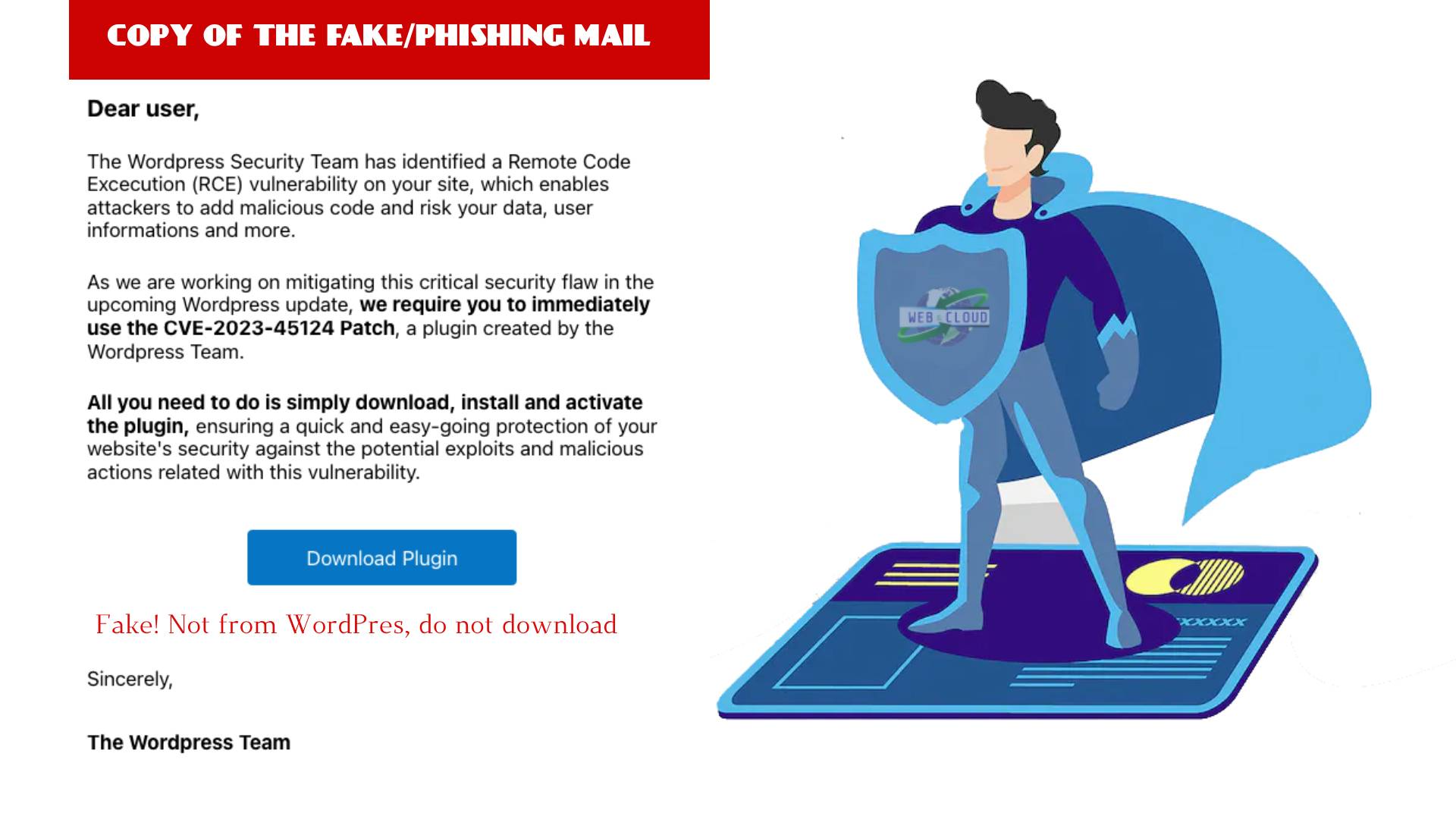
What is a wiper cyberattack?
A wiper cyberattack is a type of malicious operation where malware is used to permanently delete or corrupt data on targeted systems. Unlike ransomware, which usually encrypts data for extortion, wiper attacks focus on destroying data and disabling devices, often to cause maximum disruption rather than financial gain.
When did the Stryker cyberattack occur?
The attack is linked to events following the February 28, 2024 missile strike in Iran, which the Handala hacktivist group cited as the motivation for their wiper attack on Stryker.
Who is responsible for the cyberattack on Stryker?
An Iran‑aligned hacktivist group known as Handala claimed responsibility. The group is believed to be connected to Iran’s Ministry of Intelligence and Security (MOIS).
What type of cyberattack was used against Stryker?
Handala claims they deployed a large‑scale wiper attack, which is designed to erase data and render devices unusable. Reports suggest Microsoft Intune may have been misused to remotely wipe systems.
How many devices were affected?
The attackers claim to have wiped more than 200,000 devices, including servers, workstations, and mobile devices across 79 countries.
Did the attack impact Stryker employees?
Yes. Thousands of employees were sent home, including more than 5,000 workers in Ireland. Some staff reported that personal phones with Microsoft Outlook installed were remotely wiped.
Is the Stryker cyberattack affecting hospitals or patient care?
Early reports indicate disruptions in ordering surgical supplies and temporary shutdowns of systems like LifeNet, which paramedics use to transmit ECG data. Some hospitals have switched to radio communication as a backup.
Was any sensitive data stolen?
Handala claims to have obtained internal data, though Stryker has not yet confirmed the extent of any data theft. Investigations are ongoing.
How long will recovery take?
Stryker has not released a timeline. Recovery from a global wiper attack can take days to weeks depending on the scale of system restoration and forensic analysis.
Reward this post with your reaction or TipDrop:
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 TipDrop
0
TipDrop
0